HTB Sherlock - Heartbreaker Writeup
 HTB Sherlock - Heartbreaker Writeup
HTB Sherlock - Heartbreaker WriteupSherlock Scenario
Delicate situation alert! The customer has just been alerted about concerning reports indicating a potential breach of their database, with information allegedly being circulated on the darknet market. As the Incident Responder, it’s your responsibility to get to the bottom of it. Your task is to conduct an investigation into an email received by one of their employees, comprehending the implications, and uncovering any possible connections to the data breach. Focus on examining the artifacts provided by the customer to identify significant events that have occurred on the victim’s workstation.
Solution
Task 1
The victim received an email from an unidentified sender. What email address was used for the suspicious email?
In the directory wb-ws-01/C/Users/ash.williams/AppData/Local/Microsoft/Outlook/, there is a file: [email protected]. I used the pffexport program to analyze the file. Then, I reviewed all the messages received by the user and found the one that contained the suspicious email (Fig. 1).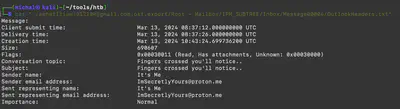
Answer: [email protected]
Task 2
It appears there’s a link within the email. Can you provide the complete URL where the malicious binary file was hosted?
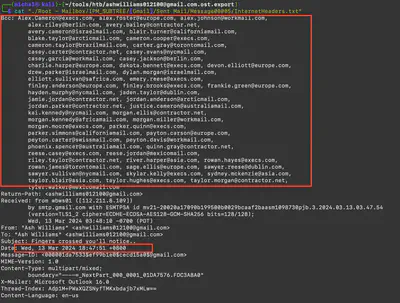
In the same directory, there was also a message (Fig. 2).
Answer: http://44.206.187.144:9000/Superstar_MemberCard.tiff.exe
Task 3
ang. The threat actor managed to identify the victim’s AWS credentials. From which file type did the threat actor extract these credentials?
Further searching through the mailbox allowed the discovery of AWS credentials (Fig. 3).
Answer: .ost
Task 4
Provide the actual IAM credentials of the victim found within the artifacts.
From the previous task.
Answer: AKIA52GPOBQCK73P2PXL:OFqG/yLZYaudty0Rma6arxVuHFTGQuM6St8SWySj
Task 5
When (UTC) was the malicious binary activated on the victim’s workstation?
In the directory wb-ws-01/C/Windows/prefetch, there is a file named SUPERSTAR_MEMBERCARD.TIFF.EXE-C2488B05.pf. To extract data from the prefetch file, I used the command PECmd.exe (Fig. 4).
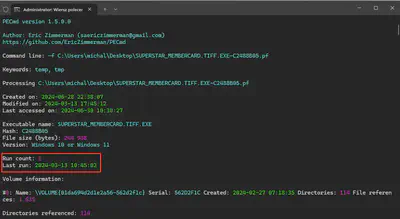
Answer: 2024-03-13 10:45:02
Task 6
Following the download and execution of the binary file, the victim attempted to search for specific keywords on the internet. What were those keywords?
First, I checked the keywords in the Edge browser (Fig. 5). The history was contained in the file: wb-ws-01/C/Users/ash.williams/AppData/Local/Microsoft/Edge/User Data/Default/History. This led me to discover that the user was also using Firefox. In the file wb-ws-01/C/Users/ash.williams/AppData/Roaming/Mozilla/Firefox/Profiles/hy42b1gc.default-release/formhistory.sqlite, I found the following searches (Fig. 6).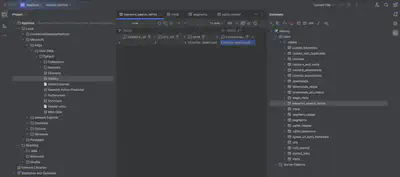
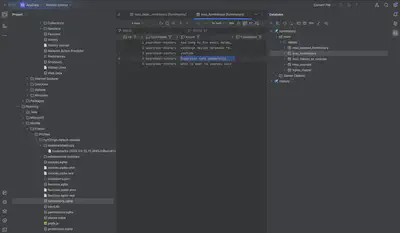
Answer: superstar cafe membership
Task 7
At what time (UTC) did the binary successfully send an identical malicious email from the victim’s machine to all the contacts?
Returning to our mailbox, we check the sent emails from the user.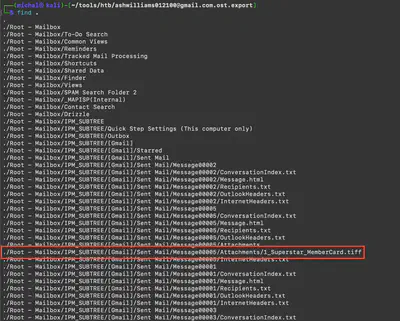
Answer: 2024-03-13 10:47:51
Task 8
How many recipients were targeted by the distribution of the said email excluding the victim’s email account?
From the previous file, we know the number of recipients.
Answer: 58
Task 9
Which legitimate program was utilized to obtain details regarding the domain controller?
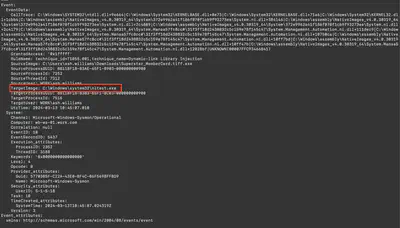
Using the command ./target/release/chainsaw search --skip-errors "Superstar_MemberCard.tiff.exe" wb-ws-01/C/, I searched for all events related to the malicious software. Tracking the identified events led to the discovery of the program (Fig 9).
Answer: nltest.exe
Task 10
Specify the domain (including sub-domain if applicable) that was used to download the tool for exfiltration.
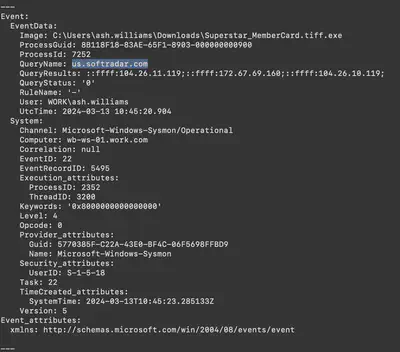
From the detected related events from the previous task (Fig. 10).
Answer: us.softradar.com
Task 11
The threat actor attempted to conceal the tool to elude suspicion. Can you specify the name of the folder used to store and hide the file transfer program?
From the detected related events in Task 9 (Fig. 11).
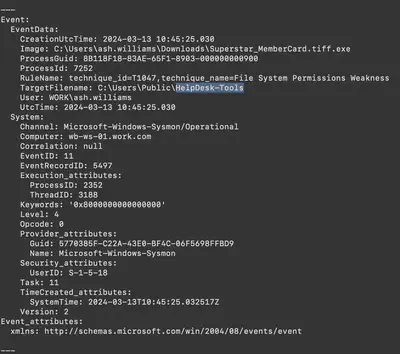
Answer: HelpDesk-Tools
Task 12
Under which MITRE ATT&CK technique does the action described in question #11 fall?
Google :)
Answer: Masquerading
Task 13
Can you determine the minimum number of files that were compressed before they were extracted?
I used chainsaw again. With the command /target/release/chainsaw search --skip-errors "Superstar_MemberCard.tiff.exe" ../htb/C/ | grep TargetFilename > files.txt, I first searched for all occurrences of the Superstar_MemberCard.tiff.exe file, then used grep to list only those files that the attacker interacted with. After gathering all the files in one place, it was enough to count those that had value for the attacker. I excluded all exe, ps1, tiff files, and discarded the HelpTools directory, as it was used by the attacker to place tools, as well as the zip file that was used by the attacker for file transfers (Fig. 12).
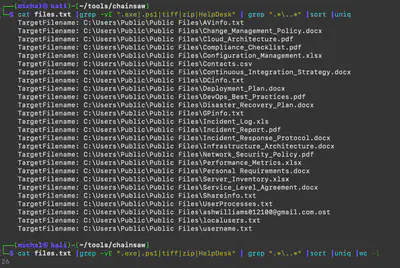
Answer: 26
Task 14
To exfiltrate data from the victim’s workstation, the binary executed a command. Can you provide the complete command used for this action?
From the detected related events in Task 9 (Fig. 13).
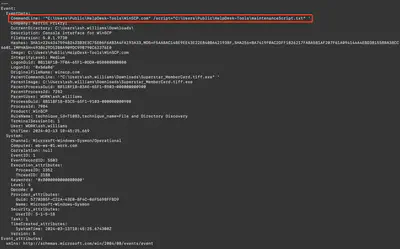
Answer: "C:\Users\Public\HelpDesk-Tools\WinSCP.com" /script="C:\Users\Public\HelpDesk-Tools\maintenanceScript.txt"